I thought this would be an interesting article to post because we used these tools in our virtual machines. The maintainers of the Linux distributions are patching a privilege escalation vulnerability, which is a major risk to the servers, desktops and other devices that use the operating system. The vulnerability has been named the Dirty Cow, it allows an attacker to gain to a limited user account to get root privileges and control the system.
Easy-to-exploit rooting flaw puts Linux PCs at risk
Want to make your own app? There are free classes for that
Hello class- while looking for something to write about I came across this article and thought I should share with you.
The New York Times has a Tech Tip section, and this week’s part by J.D. Biersdorfer walks us through the opportunities and challenges of creating apps for different technologies, even if you’ve never studied computer programming. It also provides interesting links to explore materials and tutorials for online exercises on your own pace and time.
Under the Computer Science Education Week link https://csedweek.org/, you can try to code for an hour and expand your horizon with this cool site, watch the 5-minute video and get your 5 minutes of coolness’ for the day.
There are other links available for Apple’s free software, videos and tutorials for learning the Swift language, I was also interested in the coding concepts link and the free Swift Playground app for the iPad platform, but why are you still reading this, click on the link and have fun.
http://www.nytimes.com/2016/10/22/technology/personaltech/want-to-make-your-own-app-there-are-free-classes-for-that.html?ref=technology&_r=0
Hackers Used New Weapons to Disrupt Major Websites Across U.S.
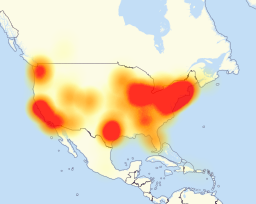
We were under attack- said the New York Times in today’s edition, based on users’ reported sporadic problems reaching several websites including Twitter, Netflix, Spotify, Airbnb, Reddit, Etsy, SoundCloud and The New York Times.
Reports from Dyn, a company that servers to monitor and reroute internet traffic said that they experienced a DDOS attack just after 7:00 a.m. Friday morning. Some users reported inaccessible sites from East Coast and it spread westward in three separate waves until evening hours.
Other reports associated to this incident mentioned that the attack appears to have relied on hundreds of thousands of internet-connected devices like cameras, baby monitors and home routers that have been infected and here is the kicker, without their owner’s knowledge, allegedly with software that allows a hackers to commend them to flood a target with overwhelming traffic.
Kyle York, Dyn’s chief strategist, said in this article that others that host the core parts of the internet’s infrastructure were targets for a growing number of more powerful attacks, and “the number and types of attacks, the duration of attacks and complexity of these attacks are all on the rise,” Mr. York said this morning.
http://www.nytimes.com/2016/10/22/business/internet-problems-attack.html?ref=technology&_r=0
How to install Advanced Intrusion Detection Environment on CentOS
We often cover topics about IDSs in class. It is a system(s) embedded within computer networks against malicious activities or policy violations. For example, an IDS infrastructure does so by analyzing incoming network traffic. However, this article titled “How to install Advanced Intrusion Detection Environment on CentOS” that I’m sharing with you provides a broader prospect about IDS, the Advanced Intrusion Detection Environment.
AIDE was developed to replace Tripwire licensed under the terms of the GNU General Public License (GPL). According to author of the article, Jack Wallen, AIDE is recommended for better I.T. Security because it serves as a supplement layer of protection for CentOS environments. For those who might be interested in learning how to deploy AIDE on a network platform the correct way, here are some detailed instruction materials of how to install AIDE on CentOS.
Access the full article via the link below:
Major websites were inaccessible to people across wide swaths of the United States on Friday after a company that manages crucial parts of the internet’s infrastructure said it was under attack.
Users reported sporadic problems reaching several websites, including Twitter, Netflix, Spotify, Airbnb, Reddit, Etsy, SoundCloud and The New York Times.
Dyn, whose servers monitor and reroute internet traffic, said it began experiencing what security experts called a distributed denial-of-service attack just after 7 a.m.
http://www.reuters.com/article/us-usa-cyber-idUSKCN12L1ME
https://community.mis.temple.edu/itacs5211fall16/2016/10/21/3717/
Euro Bank Robbers Blow up 492 ATMs
492 ATMs across Europe were blown up by thieves in the first half of 2016, as criminals looked to supplement their attempts at infiltrating machines via cyber-attacks. These “cash out” or “jackpotting” attacks typically involve malware which takes control of the ATM’s cash dispensing function to fill the pockets of the cyber criminals. ATM fraud alone cost European lenders €174m (£157m) in the first half of 2016, up from €156m (£141m) a year ago. This new shows criminal gangs increasingly using diverse tactics, and blending physical and online methods, to steal from banks. A report from Kaspersky Lab back in April claimed that almost all ATMs across the globe can be illegally accessed and raided without even the need to install malware – because they’re running outdated technology.
Link: http://www.infosecurity-magazine.com/news/euro-bank-robbers-blow-up-492-atms/
Today’s Brutal DDoS Attack Is the Beginning of a Bleak Future
The DDoS attack on 10/21/16 that took down Dyn wreaked havoc throughout the internet. Many websites like Spotify, Twitter, Paypal and many other sites were down for a significant amount of time. This goes to show that taking down a major DNS supplier can essentially take down a big portion of the internet. If hackers can do this at their own will how can we know for certain that this won’t happen again in the future even worse.
Article: http://gizmodo.com/todays-brutal-ddos-attack-is-the-beginning-of-a-bleak-f-1788071976
Dirty COW
It’s gonna be busy the next few weeks for IT Security Professionals and Linux administrators. A vulnerability that uses the copy-on-write function to perform privilege escalation can potentially allow any installed application, or malicious code, to gain root-level access and completely hijack the device.
There is also a exploit already available in the wild that makes this vulnerability even more concerning.
The fix for this is simple and can be easily addressed with two lines of code that are installed with an apt-get command. However, many organizations will need to update this in non-production environments to test before moving to production. In addition, organizations will also want to reach out to all of their suppliers to confirm that they are doing the same. Similar efforts were required for the BASH, Poodle, and Heartbleed vulnerabilities.
Lastly, make sure you update those IoT devices! Linux is a common operating system for connected home devices. They will also be vulnerable if they are not patched.
Link – http://www.theregister.co.uk/2016/10/21/linux_privilege_escalation_hole/
7 Best Social Engineering Attacks Ever
This is a great article about infamous Social Engineering attacks throughout history. The author’s tongue-in-cheek tone makes light of the intrusions, yet the damages each caused were anything but humerus. What’s very interesting about the article is that the attacks are mostly technologically based, meaning, inevitably, a hacker broke into a computer system and stole something or corrupted something but there are a few that are not. The first hack in the list dates back to the 1960s when the infamous Frank Abignale (Catch Me If You Can) used different characters to trick people into thinking he was something he wasn’t-a Trojan Horse of sorts. The article also discusses how a man was able to rob a bank without any technology at all. The only thing he deployed to obtain millions of dollars worth of jewelry was his charm. I think this is relevant to what Wade was mentioning with mingling with smokers outside of a company’s office so as to gain information. The article goes on to discuss several large hacks and how social engineering paved the road into the corrupted systems. A security analyst is quoted at the end of the article saying in so many words, “if you want to stay safe, engage end users”. Information systems are comprised, essentially, of computers, data, and end users. This article certainly suggests end users are the weakest link of the three when it comes to security.
http://www.darkreading.com/the-7-best-social-engineering-attacks-ever/d/d-id/1319411