How the NSA snooped on encrypted Internet traffic for a decade
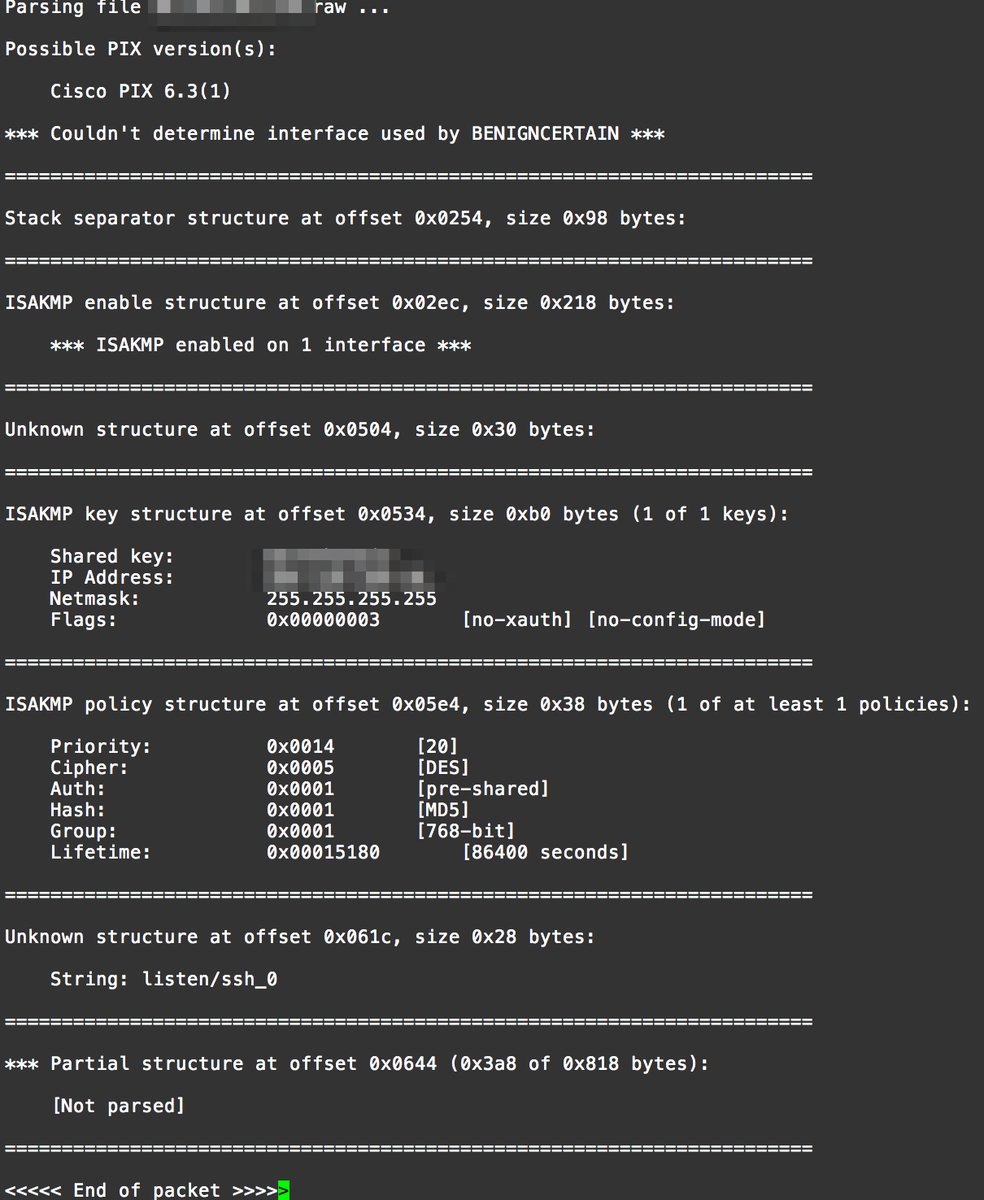
This article talks about how the NSA allegedly snooped on VPN traffic by exploiting a vulnerability in the CISCO PIX VPN> The versions that are vulnerable are 5.3(9) through 6.3(4) and were supported by CISCO from 2002 to 2009. The attack code was dubbed BenignCertain and exploits a vulnerability in Cisco’s implementation of the Internet Key Exchange, a protocol that uses digital certificates to establish a secure connection between two parties. The packets cause the vulnerable device to return a chunk of memory. A parser tool included in the exploit is then able to extract the VPN’s pre-shared key and other configuration data out of the response. According to one of the researchers who helped confirm the exploit, it works remotely on the outside PIX interface. This means that anyone on the Internet can use it. No pre-requirements are necessary to make the exploit work. The exploit helps explain documents leaked by NSA contractor Edward Snowden and cited in a 2014 article that appeared in Der Spiegel. The article reported that the NSA had the ability to decrypt more than 1,000 VPN connections per hour. The revelation is also concerning because data returned by the Shodan search engine indicate more than 15,000 networks around the world still use PIX, with the Russian Federation, the US, and Australia being the top three countries affected. The following is a screen shot of BenignCertain extracting a shared key from a Cisco PIX firewall.
View article here.
NESSUS Vulnerability Scan
Annai-senpai – Mirai botnet comments and design
After reading Jason’s post on the Mirai botnet I decided to look up the source code to get an idea of the coding involved with a botnet. They have it posted on GITHUB, and the link below is to Forum.txt, a post which was allegedly made by the botnet designer, who goes by the handle Annai-senpai. The comments are interesting, particularly when he comments on the lack of skills of his adversaries. He also gives a description of the setup used to administer and control the botnet.
Rapid-7 -The Attacker’s Dictionary
This paper summarizes a year’s worth of credential scanning data collected from Heisenberg (Breaking Bad fan’s anyone?), Rapid7’s public-facing network of low-interaction honeypots. Instead of focusing on the passwords that end users typically pick, this data contains what opportunistic scanners are using in order to test— and likely compromise— Internet connected point of sale (POS) systems, kiosks, and scamware-compromised desktop PCs which offer the Remote Desktop Protocol (RDP) service for remote management. Heisenberg honeypots are custom-engineered, low-interaction honeypots that are distributed geographically across several regions. There’s a lot of interesting statistics in this paper such as the frequency of scans from certain geographical areas, the most common usernames and passwords used in scans against the honeypots, and how these usernames passwords are associated with each other in the attack. The surprising detail uncovered was just how weak the passwords were (the most common username and password combination used was username: administrator – password: x). Since these passwords were deliberately chosen by the various scanners which ran up against Heisenberg, it implies that the default and common passwords to several POS and kiosk systems are chosen out of convenience, rather than security. Sobering stuff!
Reconnaisance Analysis – Reliance Standard Life Ins
7 Cases When Victims Paid Ransom to stop cyber attacks
This is an interesting article which talks about 7 cases where compromised ransomware victims paid to regain access to their data. The victim’s vary from police department’s to a Nascar race team. Payment was made via bitcoin, and in one of the cases, the attacks continued even after the ransom was paid. The attacks were made via DDoS attacks on an email service, and via infected computers from successful phishing scams. This article stresses the importance of security awareness training for employees, and backing up data in separate locations. Payment of ransom only encourages more ransomware campaigns so proactive solutions are imperative. The article also briefly talks about an anti-ransomware site ‘No More Ransom’‘ which was created to assist Internet users by recovering their files for absolutely free to stop them from paying ransom to criminals.
Cisco Switch Config
Hi all,
I found this video on Lynda.com and it’s a pretty good tutorial on configuring a cisco switch and setting up VLANs. It’s not long and broken up into short segments. Definitely helped me with understanding the reading for week 2.
Bilaal