-
BIlaal Williams commented on the post, Progress Report for Week Ending, February 9, on the site 7 years, 8 months ago
Thanks Menqxue,
What I gathered from the research is that forensic readiness is how prepared an organization is to handle forensic investigation.. So this would include an organizations ability to process and collect digital evidence should an incident arise. And yes, organizational forensics is the application of digital forensics within an…[Read more] -
BIlaal Williams changed their profile picture 7 years, 8 months ago
-
BIlaal Williams commented on the post, Happy Birthday SNL // the typists from the Carol Burnett show, on the site 7 years, 8 months ago
Loi,
I agree that the culture of an organization plays a significant role in how cyber threats are handled. Organizations who include cyber security in their business culture will be more likely to create policies and procedures that will allow for effective reaponse should a threat or attack arise. These organizations will more more likely to…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 10 months ago
14.1
In an emergency situation, it is definitely justified for a physician to use the most expedient method to communicate the necessary information to provide the proper care. This is why it is important to plan for these types of situations prior to prevent compromising the security of the information. If possible, a secure channel should be…[Read more] -
BIlaal Williams posted a new activity comment 7 years, 10 months ago
Acceptance of a BYOD policy is definitely dependent on the business, deciding factors include:
What are the cost benefits?
What are the risks?
Who would be allowed to bring devices?
How will devices be monitored?In organizations involving healthcare this can really present risks and a cost benefit analysis would have to be performed to see…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 10 months ago
I feel that IT professionals should definitely be allowed access to these tools as well as non-IT professionals although I know there may be some ramifications if this individual were in fact able to do harm to the system. As Mushima alluded to, your system should be hardened to the point that no lay person with access to these tools should be…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 10 months ago
As an IT professional it is still important to be prepared for a pandemic. It operations are normally required to remain in some kind of functioning state when a disaster strikes. Methods of communication are mostly IT related, particularly with organizations with offices that are a considerable distance apart. In my company, during several of the…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 10 months ago
TCP headers are used by firewalls to filter packets. TCP headers contain useful information that can be inspected by firewalls. This information will decide whether the firewall will allow the packet to enter the network. For example, when a browser sends an HTTP request to a Web server, the request contains the identity of the client computer,…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
Thanks Scott, nice tutorial.
-
BIlaal Williams wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years, 11 months ago
burpsuite powerpoint slides
burp executive summary
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
That situation would have been even worse if the temperature was considerably lower as pipes could freeze and Temps too cold could be potentially deadly. This situation shows that as the IOT begin to manage more important things in our lives cyber security becomes even more important.
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
Although quantum computing is in its early stages, enough progress has been made to determine that at some point this will become a reality. With businesses with large pockets such as Google and IBM investing in quantum computing development, it seems likely that quantum computing will come into fruition, just how long it takes remains to be…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
Kerckhoffs second axiom, which states a cryptosystem should be secure even if it falls into enemy’s hands, remains relevant today in modern cryptography and alludes to the fact that an effective cryptosystem should be secure even if everything about the system, except the private key, is public knowledge. This axiom provides the basis for public k…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
When dealing with applications I feel whitelisting is an easier method to maintain, as you can create a list of known applications and update the list as needed when knew applications require access to the system. All other applications will be blocked. Although compiling and maintaining the whitelist may be difficult, it is better to put in the…[Read more]
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
When dealing with applications, I feel whitelisting is an easier method to maintain, as you can create
-
BIlaal Williams posted a new activity comment 7 years, 11 months ago
Good point Jason, I wasn’t thinking along those lines but it is quite possible that the vulnerability was intentionally planted as a back door..
-
BIlaal Williams wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years, 11 months ago
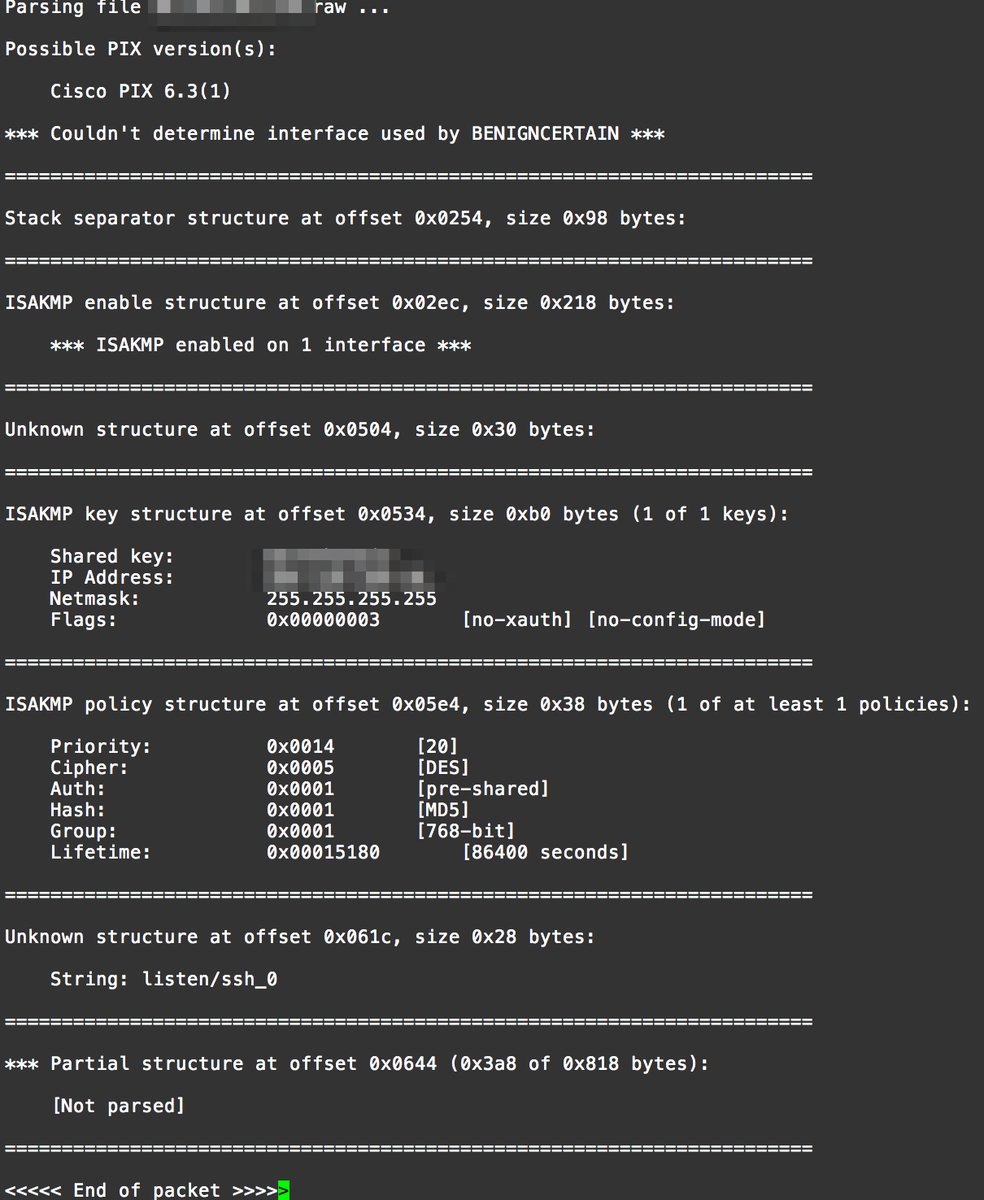
This article talks about how the NSA allegedly snooped on VPN traffic by exploiting a vulnerability in the CISCO PIX VPN> The versions that are vulnerable are 5.3(9) through 6.3(4) and were supported by CISCO […]
-
BIlaal Williams wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years, 12 months ago
vulnerability_summary
nessus-vulnerability-scan
-
BIlaal Williams wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 8 years ago
After reading Jason’s post on the Mirai botnet I decided to look up the source code to get an idea of the coding involved with a botnet. They have it posted on GITHUB, and the link below is to Forum.txt, a post […]
-
BIlaal Williams commented on the post, Weekly Question #8: Complete by November 2, 2017, on the site 8 years ago
Also, releasing the source code once the Feds are on to you ensures that the source code is in many different places which makes it harder for the authorities to pinpoint. So far I haven’t experienced any symptoms, but I definitely feel that access to the source code is a good way to see how these DDoS attacks work.
- Load More
Connect and innovate with an elite information systems program
Footer
MANAGEMENT INFORMATION SYSTEMS
Fox School of Business
Temple University
210 Speakman Hall
1810 N. 13th Street
Philadelphia, PA 19122
