-
Fraser G commented on the post, Week 7 Update, on the site 6 years, 7 months ago
I just tried with Webex player and didn’t have any luck with that either.
-
Fraser G commented on the post, Week 7 Update, on the site 6 years, 7 months ago
Satwika-
Thanks for putting this up however I am not able to open it – some WRF file format that isn’t recognized.
What do you use to open these?
-
Fraser G commented on the post, Week 3 Update, on the site 6 years, 8 months ago
Freddy-
Does the white paper mention anything about redundancy for storing logs? On site sounds great but I would think having another copy is important. As we have learned in this program, malware and attackers will overwrite logs to hide suspicious activity.
And how about logging access to the logs? I need to read this white paper.
-
Fraser G commented on the post, Week 3 Update, on the site 6 years, 8 months ago
These are really useful, thanks Freddy!
-
Fraser G commented on the post, Course Work, on the site 6 years, 9 months ago
Testing,.,,,
-
Fraser G commented on the post, Week 2 Update, on the site 6 years, 9 months ago
Mustafa-
Nice summary. One million file submission a day for Virus Total. Seems kind of low to be honest. Is the idea to get everyone using some sort of open standard for virus comparison to keep them from spreading? If so I can get on board with that – would need to be able to scrub any sensitive data however or have a trusted authority to do this.
-
Fraser G commented on the post, Ai.type Keyboard Collecting Data, on the site 6 years, 10 months ago
Part of the problem is that app developers know that very few users understand/read the ToS when they accept “Share my information” on these sorts of apps. I have been trying to educate my friends and family to take a more skeptical view of these kinds of things. That great maxim “If you are not paying for it, you’re not the customer; you’re the…[Read more]
-
Fraser G commented on the post, Discussion Week 2, on the site 6 years, 10 months ago
The biggest benefits of Single Sign On (SSO) are 1)Decreased “friction” in user experience when authenticating (one credential versus many); Decreases total cost of ownership for SSO – AWS just rolled out there own – for smaller companies; last a single point of management for systems administrators (potentially).
The biggest risks and threats…[Read more]
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 6 years, 11 months ago
Last week Matt Blaze gave a presentation before congress related to hacking elections. I have linked both the article and the testimony. The testimony is interesting to read and isn’t very long, here is an […]
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 6 years, 11 months ago
This week is all about authentication, and I have two related articles about authentication:
and
In short, Facebook is testing a captcha test that requires the user to upload a selfie to authenticate, and in […]
-
Fraser,
I do believe protecting usernames and passwords very important to insure the continuity of any business. We will continue seeing new methods to access our accounts. In my opinion, some arts to produce and design new login methods will be very helpful to break down the algorithms that attackers develop everyday to attack people.
-
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 6 years, 11 months ago
Another article about Equifax, ho-hum. Except this one is the BEST summary of the attack I have found that is accessible to people who don’t have a lot of technical expertise but know a bit about cybersecurity a […]
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 6 years, 12 months ago
Curve25519 and Curve448 will be added to the NIST SP 800 this year as new curve schemas for elliptical curve encryption.
Curve25519 is an elliptic curve Diffie–Hellman and uses the equa […]
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years ago
Interesting article about security related to CA’s and private equity. It sounds like this industry is a target for consolidation, or at least a shakeup with the private equity guys getting involved. In […]
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years ago
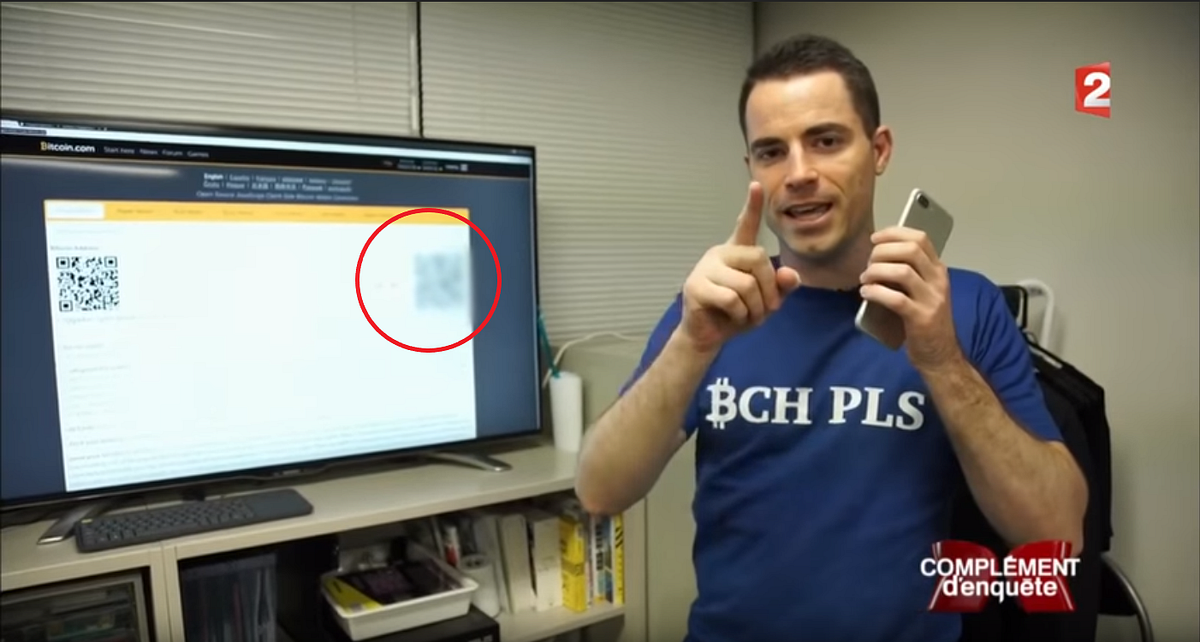
This article is a demonstration of why you should always be very careful when sharing any information publicly. The authors of this article detailed a process of image correction and QR code “hacking” to figure […]
-
Fraser,
Your article is quite interesting and upon reading I was actually shocked to see such threats possible. You are right when you say that Information should not be disclosed publicly, but practically it is impossible for high profile people to not disclose or hide everything. The Image correction of QR code hacking is pretty shocking because if we consider China or United States, these countries use digital QR currency payments in almost 90% of their every transactions. How much will QR code hacking unfold itself further and what will be its impact across different channels that use QR code or user’s Identity codes for validation?
-
-
Fraser G commented on the post, WPA2 Cracked, on the site 7 years ago
I hear you Fred. I already patched my WAP and router with the latest beta drivers. Getting others to patch is the big problem… I wonder if Starbucks is already updated? How about hotels? Lots of opportunities for bad actors.
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years ago
WPA2 encryption has been compromised. KRACK Attacks or Key Reinsallation Attack allows hackers to decrypt packets in Wifi traffic and … “use this novel attack technique to read information that was […]
-
This is pretty scary since WPA2 is the wireless security currently in place for almost all Wi-Fi networks. I know at Verizon old routers still operate on WEP and they applied a firmware update to make sure they operate on WPA2 or we replace it. But to hear it has been cracked, make me a little paranoid about my info I send over the network and if someone is trying to crack it.
-
Frazer,
I read about this yesterday as well. It is a bit scary, but the patch was released and “fixed”. This is a man-in-the-middle attack. This is a big issue, but the problem for the “bad guys” is that they would have had to been in your WiFi range to get any of the information.
Add a compensating control to your house and do a quick search of the WiFi perimeter before sending sensitive data… But I guess that would mean when someone is walking around their house, they may be about to use their credit card on-line. We can’t win…
-
I hear you Fred. I already patched my WAP and router with the latest beta drivers. Getting others to patch is the big problem… I wonder if Starbucks is already updated? How about hotels? Lots of opportunities for bad actors.
-
-
Hi Fraser:
Interesting article but at he same time pretty scary because WPA 2 is the wireless security for most of Wi-Fi.
-
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years ago
This article from Threatpost.com details Formbook, a malware that can be spread in PDFs, DOCS and XLS files. The malware has been on sale since July for the low price of $29/week. It is primarily a data stealing […]

-
Fraser G commented on the post, Massive Data Breach in India, 6000 Businesses Compromised, on the site 7 years, 1 month ago
Matt-
Interesting article. I wonder what effect this will have on all of the outsourced IT to that region? Also, when are we going to start hearing from about breaches from compromised organizations first, and not from the stolen data providers?
Fraser
-
Fraser G wrote a new post on the site ITACS 5211: Introduction to Ethical Hacking 7 years, 1 month ago
Russia have been given the source code to ArcSight, a cyberdefense system used by the Pentagon and US intelligence. Experts and former employees say the source code review is a huge security blunder:
“Six former […] -
Fraser G posted a new activity comment 7 years, 1 month ago
Good question! Probably all managed by lawyers and PR specialists, who abide by whatever regulation is in place.
- Load More
Connect and innovate with an elite information systems program
Footer
MANAGEMENT INFORMATION SYSTEMS
Fox School of Business
Temple University
210 Speakman Hall
1810 N. 13th Street
Philadelphia, PA 19122
